Yes, Red Team is sexy, I’m a Red Teamer and it’s the Hype!!. Who doesn’t like the rush of being a bad guy and hacking into a Network Infrastructure while trying to be as OPSEC on a Network.
I’ve known a few Offensive Researchers that have some sort of a Blue Team background, they all needed to understand an Active Directory, a Cloud Network, Servers, Workstations, Network Traffic to be a great at Red Team and move around these defenses they used to work with.
I want to point out these “Defenses” that the Blue Team uses to locate a Red Team or (malicious) activity. As great and automated that they are. they aren’t 100% reliable. I can’t say this enough as it’s always a good rule of thumb for anyone trying to Red Team specially when we want to consider some Evasion.
Understand your tools.
I wrote a blog about understanding SMBEXEC at a very high level to bypass detection from an AV standpoint, in terms of its behavior and static analysis. This made me realize and appreciate the work that goes behind these tools for Red Team and the detection’s that Blue Teams have to go up and work on. I want to explain in a Red Team standpoint why we should understand our fellow Blue Team, not in a bad way but to make the Red Team a little more fun and help the Blue Team see how we think in terms of their detection’s.
I think many of the Cyber Security realm have encountered the “Oh it’s Detected by [AV], why?!?!”. Well these users don’t understand the Red Teams Job or are mostly beginners in the Cyber Security space.
I want to approach a tool called Persistence Sniper by @last-byte. The tool caught my interest as this is meant to aid in catching malicious activity specially on the Persistence area.

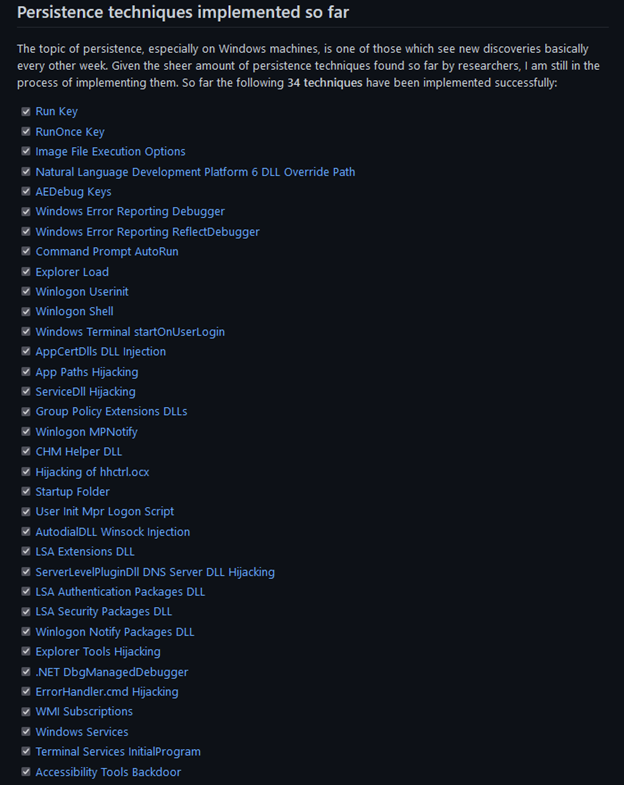
Let’s begin the tools explains what techniques are implemented and are detected by this, since this is one guy and open source. Don’t expect that this is a one in all solution, if we remember in “The Why” section it’s explained that it was suited for the developer but made the effort to make a friendly for everyone. There are currently 34 techniques that are implemented.
Let’s run the tool on a clean box and take a look at what the tool see’s.
This shows some false positives these alerts do exist but aren’t malicious. Now let’s add a malicious persistence.

Take a look at the new output showing us the Persistence Technique being utilized here.
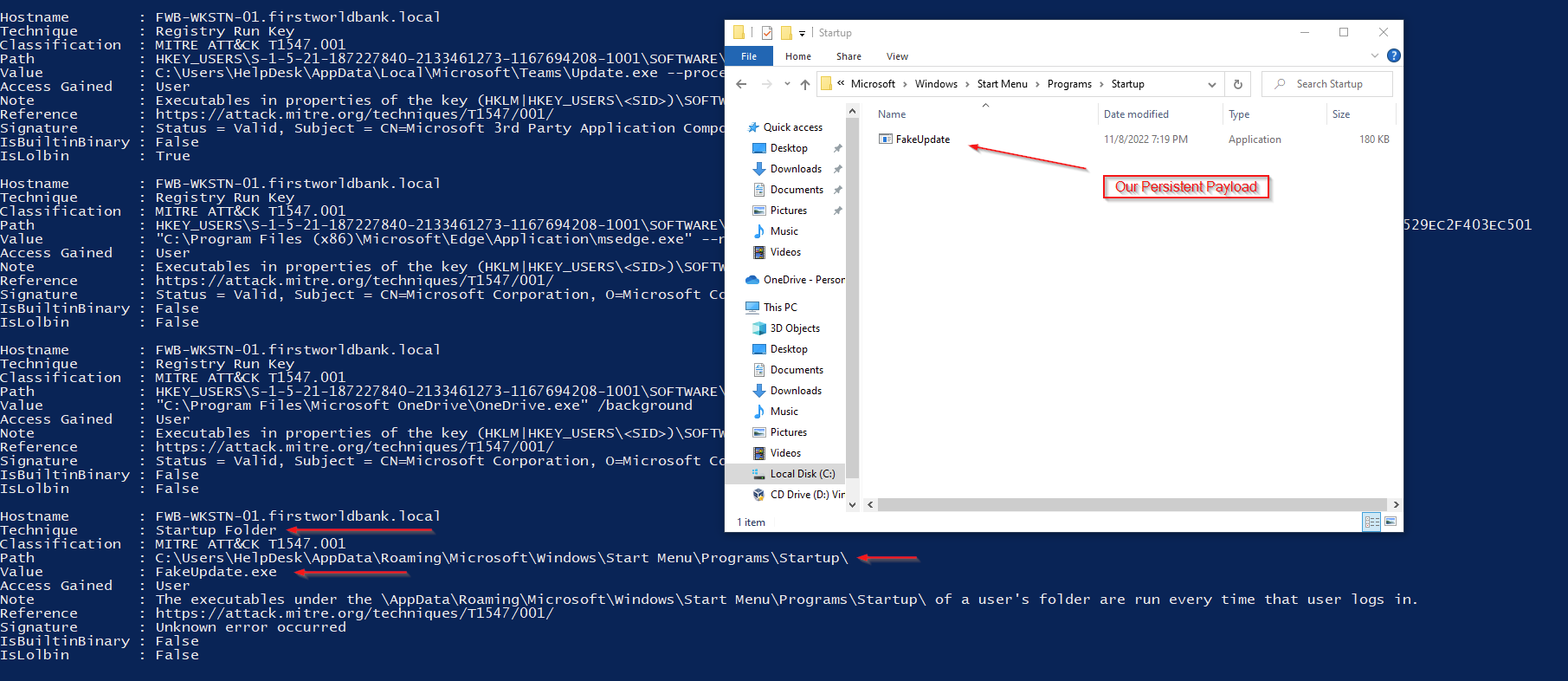
The data shown is great for an analyst. We can take a look at some valuable information about the technique, it will give us the Name, the Classification with MITRE, the Path of where it’s located and if it has a Signature.
Let’s take a look at the code here, these are the parameters which we can use to search for 1 specific or all techniques there is a technique that isn’t here which we will apply next, and those are PowerShell Profiles.
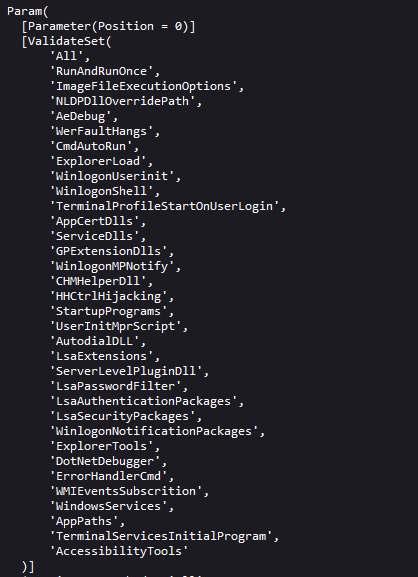
I see something about Terminal Profiles no clue what that is, but hey I learned something.
This is why it’s good to understand the Blue Team the tools they use, the procedures they take and the stuff they know and look for.
Applying a PowerShell profile persistence technique the tool doesn’t catch it

Now every time a user loads PowerShell our payload will get executed

I wanted to give in understanding on why we need to understand our tools, and be in Zen with the Blue Team. We aren’t here to argue and complain about each other, were mostly here to help each other and understand both the Offensive and Defensive side of Cyber Security. Even though it’s not always that way it’s still good practice for anyone trying to understand why our tools get caught.
What better way to bypass protections if you don't understand how they work???. How can you protect if you never get a challenge not everyone uses metasploit.