Today I will talk about persistence, the technique used by adversaries to maintain their foothold on your network. It mainly consists of techniques used by adversaries to keep access to systems across restarts, changed credentials, and other interruptions that could cut off their access.
Many tools are great for these techniques and I will demonstrate a few simple one’s to get started you can always research for more advance methods and techniques, and probably other tools than can aid in being stealthy across the Network. Try to learn as many methods as possible with a C2 and without it. Most commonly since you are a Red Teamer you will be using some sort of C2 for your Shells.
I am not trying to be stealthy here I will just demonstrate the ways we can keep our Access onto the System.
I will work with some very easy ones, some of these samples you can find on my GitBook, MITRE and other great sources .
I will work with a regular shell but try to learn this as well to keep your persistence using a C2. I will start with a Simple One.
Shortcut Links
The easiest to work with and sometimes very effective, workers rely on Shortcut Links or sometimes have no idea that they create this, to access their files “Faster” (for what I heard) so why not trick them to running our Shell and Execute code.
It’s easy to follow in this Method.
Right-Click >> New >> Shortcut
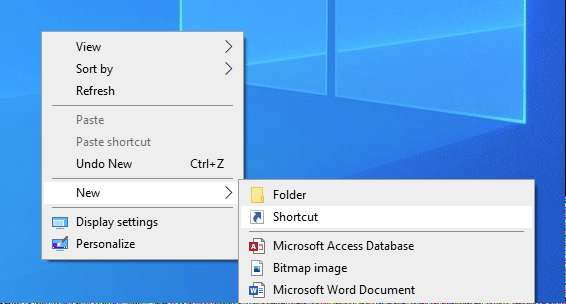
Then Right Click >> Properties >> Add your Code Here
Optional: You can change the “Start in:” and your Shell will start in that Directory. To change the Icon just Change Icon >> Find the Path for the ICO file and Select then you are good to go.

Once it’s clicked you will gain a Shell and their Link just won’t do anything “Almost” in the background it will execute a PowerShell command to call your Shell in Memory.
Perfect the Command executed and gain us our Connection. No Flags, No AV. Very easy to use and have a quick Persistence technique running on the Target System. A quick and Simple Technique yet effective when applied correctly on environments that can be easily tricked.
Scheduled Tasks
Another great method to gain Persistence on the Target Machine it’s great since this is another method that does not require any High Privileges such as Administrator or SYSTEM. You can work with a User permission scheduled task an still have Persistence, these are easy to work with but the majority would like to have Persistence as an Administrator on the System but let’s create a quick show on how to keep our Access using a Scheduled Task.
The great thing about this is you can have the Task execute commands or executables whichever you prefer in this occasion I will use a Binary which will call my Payload in PowerShell to keep Myself in Memory as well.
First I will need to Drop my Binary onto the System, use any method here that you are more familiar with usually C2’s can help or many of the LOLBINS available to execute this, I will simply use PowerShell Invoke-WebRequest.
To create a task we use the following command:
schtasks /create /sc minute /mo 1 /tn "Windows Updates" /tr "PATH"
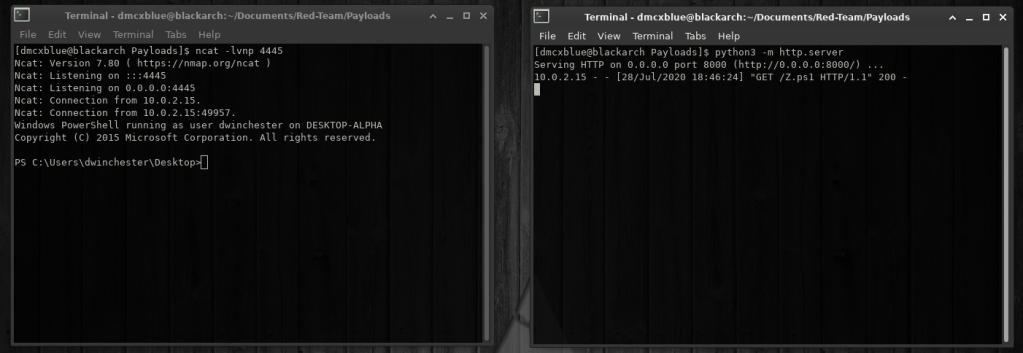
I verify my task named Updater and I can tell it was successfully created to run every 1 Minute. I will go back to my Attacker Box and start a listener on the Port that I know my Payload will connect back to.

And that easy a Persistence Shell with User Privileges by creating a simple scheduled task running every minute to call our Payload and Connect to our Specified Port (Running in Memory as well as this C# Binary calls PowerShell and uses and Obfuscated Payload to do all this, no need to do this as I am only teaching Basics).
PowerShell Profiles
PowerShell Profile is a PowerShell script which you can customize to your environment and add session specific elements to every PowerShell session that you Start.
Its a script that runs when PowerShell starts. You can use profiles as a logon script to customize the environment. You can add Commands, Functions, Aliases, Modules, etc.
PowerShell supports several profile files. Also, PowerShell host programs can support their own host-specific profiles.
A few Samples:

The PowerShell profile script is stored in the folder “WindowsPowerShel” which is by default is hidden from the user. If a payload has been dropped into disk the “Start-Process” cmdlet can be used to point to the location of the Executable. The “Test-Path” determines if a profile exists for the current user. If the profile doesn’t exist the Command “New-Item -Path $Profile -Type File -Force” will create a profile for the current users and the “Out-File” will rewrite the profile.
First let’s create a Profile:

Then I will add the command I want to be executed when a New PowerShell Session is initiated.
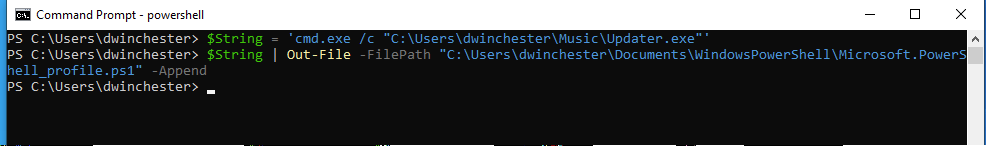
Now every New PowerShell will run my Executable Command and connect back to my Attacking Machine.

These are just a few demonstrations that I wanted to share they are simple and very easy to follow, If you would love to go more into Detail please do check out the MITRE FrameWork as it’s a great guide to understand and check out various techniques used by APT’s.
Keep hacking!!
References: